Happy New Year 2020!
Wow, 2020. Seems so futuristic.
When I was a kid in the 1970’s 2020 seemed so far away with it’s underwater cities and moon bases. Here it is and we don’t live underwater or on the moon. Instead we’ve expanded to living in tents on sidewalks or under freeway overpasses.
But I’m not going to turn this into social commentary. I am, however, going to take a look at the past 10 years and how much things have changed for my family. Way back in 2010 I was building my second airplane with the help of my kids. I did the majority of the work but they did help on many components.

We were attending church at Central Valley Presbyterian where I was a deacon. Also, Cristy had to make an emergency trip back home to the Philippines because her father passed away. That’s how the decade began.
In 2011 I sold our pop-up tent trailer in which I had taken the family on several camping trips. The most memorable of which was Zion Canyon National Park. I also flew the Rans S6 to Oshkosh, WI for EAA Airventure. My oldest graduated high school.

In 2012 we took a family trip to Maui. Yep, all of us, mother-in-law included. However, my daughter had broken her ankle just prior to the trip… and then came down with a cold! She didn’t get to have much fun in Hawaii, poor thing. But she made up for that later.
In 2013 life was pretty much on auto-pilot. Going to work, going home. Home-schooling our daughter was coming to an as we put her in a private school so she could get some socialization and a real-live high school diploma. Two kittens named Jovie and Truffles showed up in my son’s pockets one day when he came home. Truffles still lives with us. Jovie moved on shortly after he came to live with us. Cristy and I also took a trip to Oregon to celebrate our 25th wedding anniversary.


In 2014 I was beginning to explore full-time RV living. I started coming up with a plan to travel from property to property for my employer to do network work. However 2015 would put an end to those dreams, temporarily.
2015 was a harbinger of change for our lives. Our daughter graduated from high school and we changed churches.

2015 was also when I had an accident in my airplane. I landed up in the Sierra Nevada foothills and took the landing gear off. Hey, it could happen to anybody! Unfortunately, it happened to me. We got a big insurance settlement and everything was good. I was putting the airplane up for sale anyway. It was at this point Cristy and I were seriously looking at RV’s so I was looking for a more portable form of aviation. I found it in the form of powered paragliding.
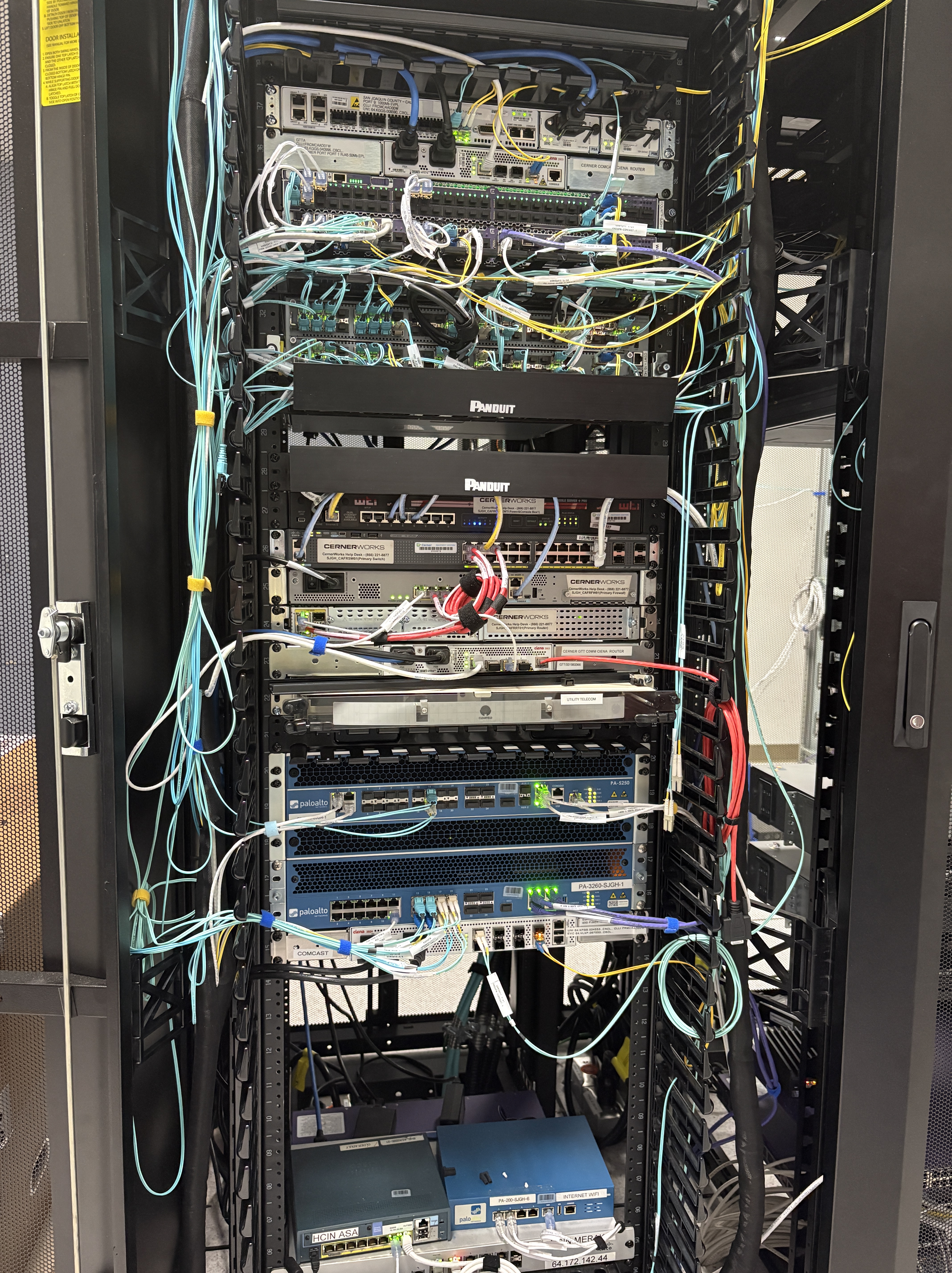
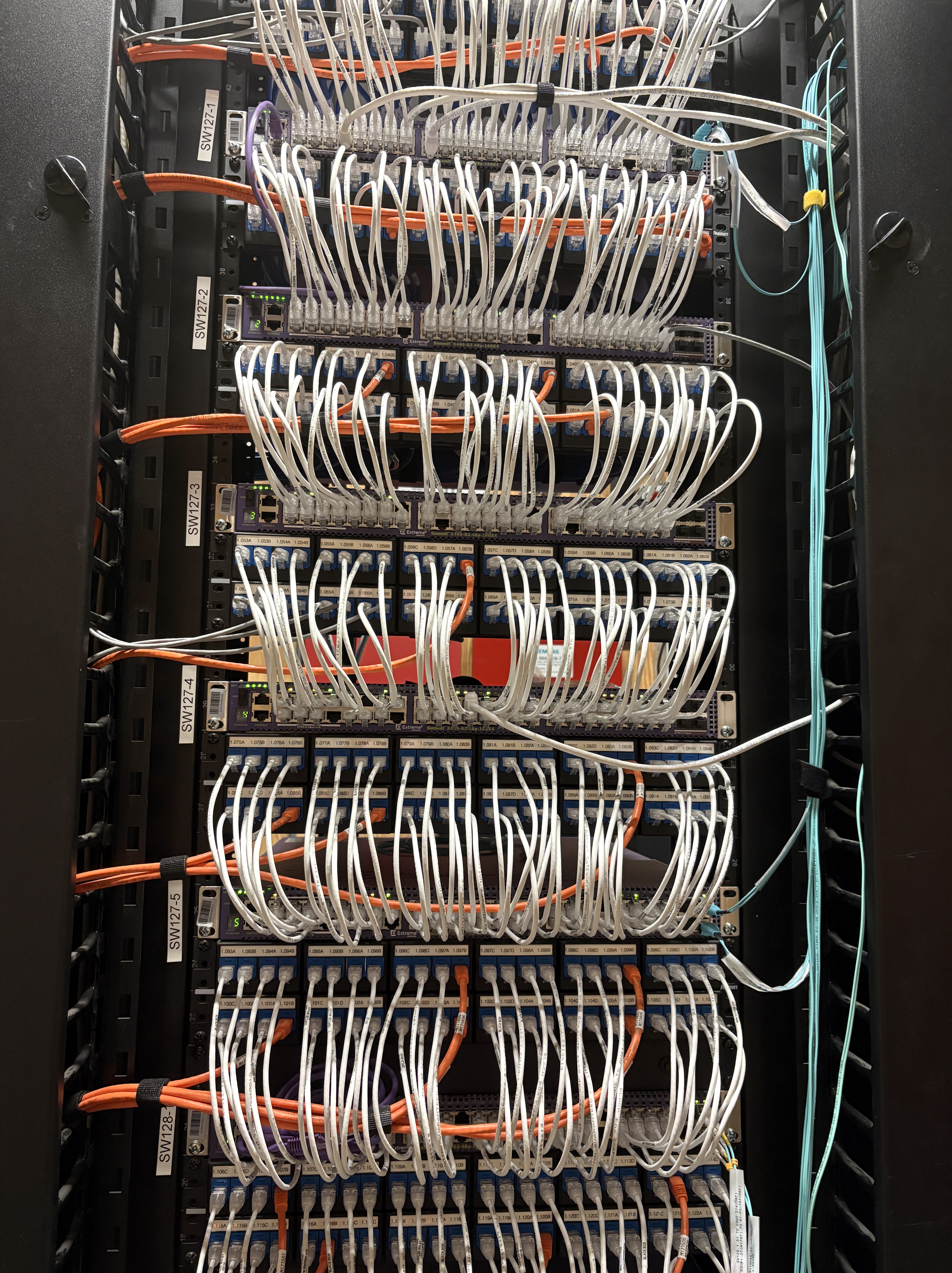
2016 was a gut punch. I was told that my entire department would be laid off that year. Also my son was going through some extreme behaviors. It seemed like my life was about to hit rock bottom. SEEMED. We started putting my son in group homes which he kept getting kicked out of due to his behaviors. But 2016 was the year God truly moved in our lives. He found a home that was able to really work with my son. And He found me a job. This is when I started working at San Joaquin General Hospital. To celebrate my getting a job we took a family road trip to SoCal. I also got a Ham radio license so I could legally use a Ham radio on my powered-paraglider.


In 2017 life started getting somewhat better for us. My son was living in a home only 5 miles from where I worked. My daughter was getting very involved in church and starting college. Cristy and I also celebrated our 30th anniversary in Hawaii.
Also, Angela finished the Spartan Race

By 2017 I had sold my powered paraglider and had bought my powered parachute. Cristy and I had also started walking more, trying to get in shape.
2018 was another year that brought a lot of change. Mostly in me. Through walking and intermittent fasting I was able to lose about 50 lbs.
This is me just prior to losing weight…

And this is what I looked like post weight loss…

2019 was a sad year. We lost my sister Sheila to cancer. We lost my wife’s cousin Jaime to kidney disease. I was diagnosed with invasive malignant melanoma.
2019 was a happy year because we became part of a small group at our new church. We received a lot of support from them and they came along side us in prayer many times. The doctors were able to remove all of the melanoma. I also sold my powered parachute and began flying rental airplanes. I got back into regular airplanes after a young man from my old church took me for a ride to pay me back for all those times I took him for rides when he was learning to fly. Now we fly together whenever we can.

2019 ended with my son being removed from a bad living situation in the group home he was in. He now lives back in town with us, which, he has been asking for quite some time. My daughter also bought a poodle this year.
It’s been a tumultuous decade. We’ve covered a lot of territory in the last 10 years. Who knows where we’ll be 10 years from now. Not sure but I sure like where we are now. I wouldn’t trade a second of the last 10 years for anything. I’ve seen God’s faithfulness and Providence countless times. I see God’s love in those around me every day. I don’t expect that to change much. I’ll keep doing what I can to reflect God’s love to those around me.


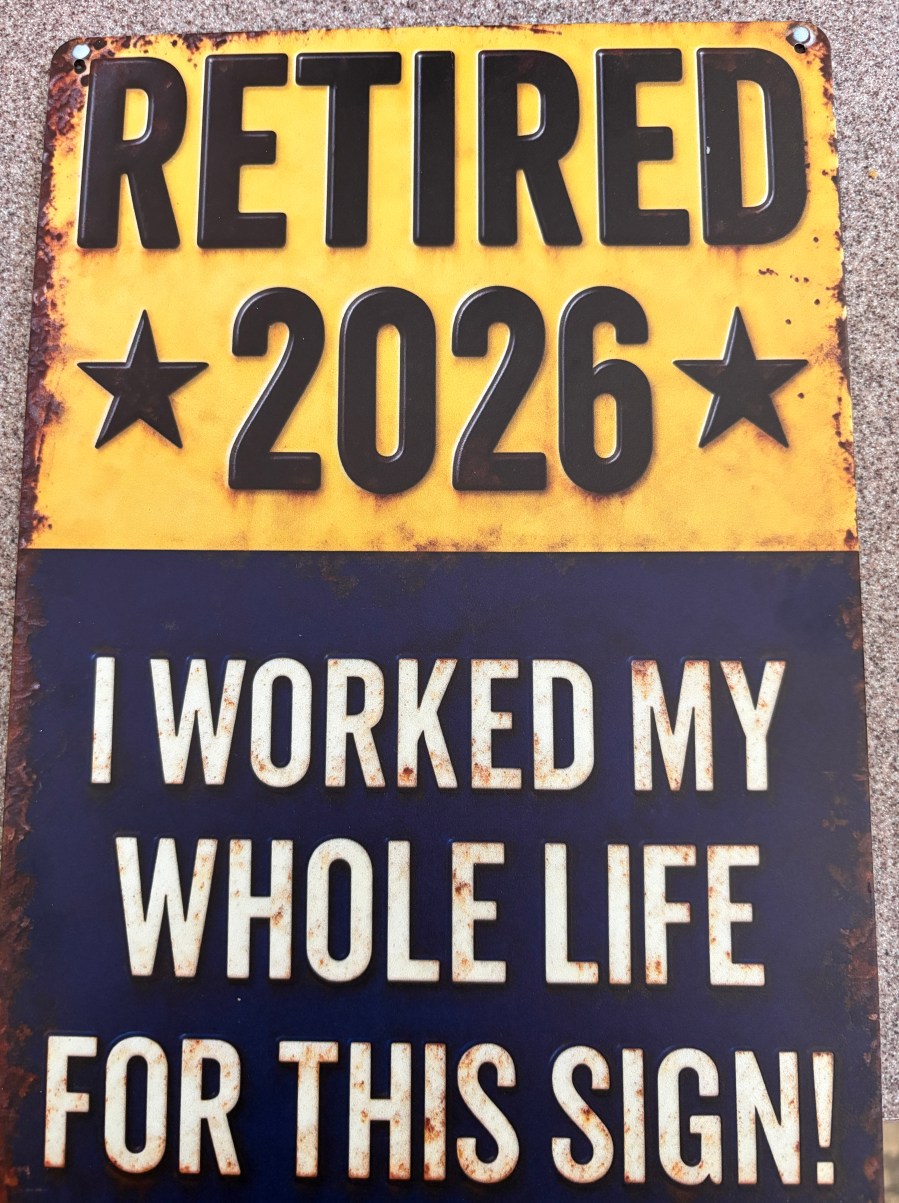



 After 18 years of reliable service we decided it was time to put our 1998 Toyota Sienna out to pasture. I knew that I wanted a Ram 3500 to be our tow vehicle when we eventually start travelling full time. I also knew that we won’t be able to live that lifestyle for another 7 to 10 years. There would be no point in having a Ram 3500 as my daily driver for the next 7 years. But I also knew the Sienna wasn’t going to last another 7 years. After discussing it with my wife she suggested I get an interim truck. After searching around a little I finally settled on a bare bones Ram 1500. This particular truck has storage compartments on either side of the bed, and basic instrumentation. I went basic so the truck wouldn’t be an attractive target for thieves.
After 18 years of reliable service we decided it was time to put our 1998 Toyota Sienna out to pasture. I knew that I wanted a Ram 3500 to be our tow vehicle when we eventually start travelling full time. I also knew that we won’t be able to live that lifestyle for another 7 to 10 years. There would be no point in having a Ram 3500 as my daily driver for the next 7 years. But I also knew the Sienna wasn’t going to last another 7 years. After discussing it with my wife she suggested I get an interim truck. After searching around a little I finally settled on a bare bones Ram 1500. This particular truck has storage compartments on either side of the bed, and basic instrumentation. I went basic so the truck wouldn’t be an attractive target for thieves.